Verify Call Record Entries – 7572189175, 3715143986, 081.63.253.200, 097.119.66.88, 10.10.70.122.5589, 10.24.0.1.71, 10.24.1.533, 10.24.1.71/gating, 111.150.90.2004, 111.90.150.1888
In assessing Verify-Ready Call Records, the entries listed—spanning numeric figures and IP-like identifiers—invite a methodical inspection of determinism, timestamps, and metadata. Their value rests on traceable sources, destinations, and contexts that support auditability. Cross-checks against network traces should confirm path integrity while flagging formatting or spoofing anomalies. A scalable workflow promises reproducible validation, yet gaps may emerge, leaving the reader poised to pursue deeper verification steps. The next phase will illuminate concrete applicability and potential edge cases.
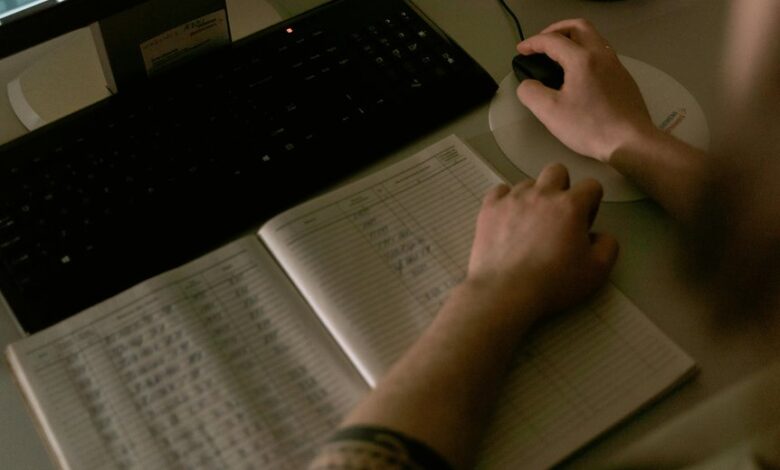
What Verify-Ready Call Records Look Like
Verify-Ready Call Records are structured to enable reliable verification by auditors and systems. The format emphasizes deterministic fields, timestamp integrity, and standardized identifiers. Each entry presents source, destination, and context with concise metadata, ensuring traceability. Verification-ready data reduces ambiguity, supports audit trails, and enables automated checks. Terms like verify ready and call records anchor consistent interpretation across independent evaluators.
Cross-Checking Logs Against Network Traces
Cross-checking logs against network traces involves aligning recorded events with their corresponding packet-level paths to confirm consistency and timing. The process emphasizes call integrity and precise data reconciliation, ensuring traceability from endpoints to gateways. Analysts compare sequence numbers, timestamps, and routing changes, isolating discrepancies promptly while preserving auditability and compliance, without conflating call details with unrelated traffic or artifacts.
Spotting Anomalies and Red Flags in Entries
Anomalies in call record entries can signal data integrity issues or security concerns, and their detection requires a disciplined, metric-driven approach.
The analysis centers on identifying deviations from baseline patterns, abnormal timestamps, inconsistent formatting, and unusual caller/receiver pairs.
Detecting anomalies relies on thresholds and correlations, while red flags indicate potential manipulation, spoofing, or unauthorized access needing further verification.
Practical Workflows for Verification at Scale
Organizations adopt scalable verification workflows by systematizing data quality checks, audit trails, and access controls across large volumes of call records.
Verification workflows enable repeatable validation steps, automated anomaly reviews, and traceable outcomes.
Pragmatic practices emphasize modular tooling, continuous monitoring, and centralized governance.
Scalable auditing supports independent verification, reproducible results, and transparent accountability while preserving operational flexibility and freedom to adapt methodologies.
Conclusion
In conclusion, verify-ready call records embody deterministic fields, consistent timestamps, and context-rich metadata that enable traceability and auditability when cross-checked against network traces. The methodical workflow supports scalable, reproducible validation and modular outcomes. Any anomaly—formatting quirks, spoofing indicators, or path deviations—triggers targeted investigation. Through disciplined documentation and repeatable procedures, auditors gain confidence in integrity. Like a meticulous archaeologist with a digital compass, the system preserves provenance across sprawling, interconnected traces, even amidst a brass-bound xkcd-era abstraction.



