Validate Incoming Call Data for Accuracy – 3533982353, 18006564049, 6124525120, 3516096095, 6506273500, 5137175353, 6268896948, 61292965698, 18004637843, 8608403936
A disciplined discussion on validating incoming call data begins with identifying source provenance and aligning timestamps across fields. The process must separate true signals from noise through anomaly detection and thresholding while enriching records with contextual attributes that do not obscure core values. An auditable lineage and versioned changes are essential to sustain governance. The outline invites concrete workflows, but the practical implications and edge cases warrant careful examination before proceeding.
What “Validating Incoming Call Data” Means in Practice
Validating incoming call data in practice involves establishing a clear protocol for what constitutes acceptable data, how it is checked, and how discrepancies are handled. The process emphasizes reproducibility and traceability, with documented validation steps and audit trails. Attention to validation pitfalls ensures consistent outcomes, while data enrichment may augment records, enhancing context without obscuring core attributes or introducing bias.
Core Checks That Separate True Signals From Noise
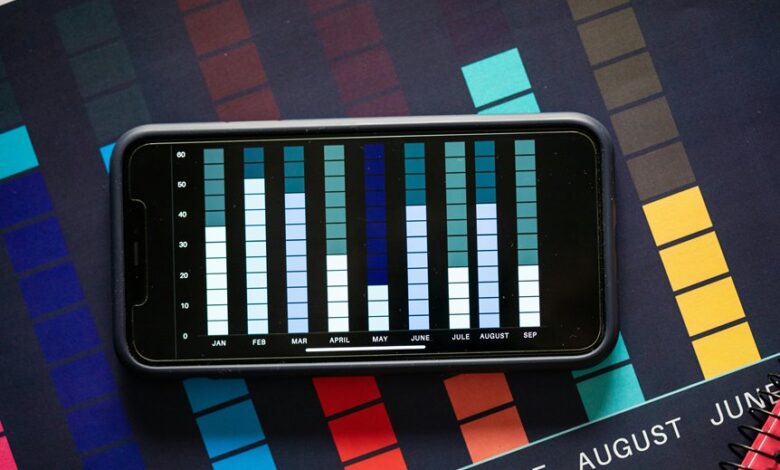
Core signals emerge only after data are subjected to a defined sequence of diagnostic checks designed to separate meaningful patterns from random variation. The checks emphasize contextual accuracy and data provenance, verifying source integrity, timestamp alignment, and cross-field consistency. Noise is filtered via thresholding and anomaly detection, ensuring that retained signals reflect reliable, traceable origins and coherent contextual relationships.
Enriching Call Data for Reliable Metrics and Decisions
Emphasis rests on data quality and metric reliability, with scalable checks ensuring consistent outcomes across varied sources and analytical pipelines.
Practical Workflow to Implement Validation at Scale
Efficient validation at scale begins with a formalized workflow that translates raw call events into verifiable, auditable data assets.
The workflow codifies input checks, lineage, and versioning, enabling repeatable validation.
Anomaly detection flags suspicious patterns, while routine checks catch invalid data.
Automation reduces human error, ensuring scalable, transparent governance and auditable evidence for stakeholders and regulators alike.
Conclusion
The validation workflow for incoming call data emphasizes provenance, temporal alignment, cross-field consistency, anomaly detection, and auditable lineage. A concrete case illustrates the value: a telecom provider uncovers a surge in calls flagged as high-risk when timestamps diverge from log sources, prompting an immediate audit trail and corrective action. By enriching context without masking core fields, and maintaining versioned lineage, the process yields auditable, bias-resistant metrics suitable for governance and decision-making.



