To Know About puwipghooz8.9 Edge
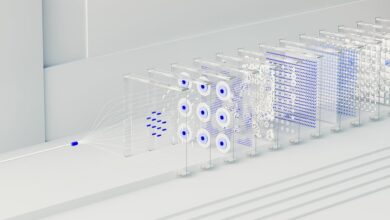
puwipghooz8.9 Edge represents a provisional, architecture-focused approach that blends near-data processing with centralized control. It aims to reduce latency and bandwidth use while strengthening security and governance through robust orchestration and standardized interfaces. Real-world viability hinges on clear governance, measurable performance, and cost trade-offs. The concept invites careful evaluation of risks, governance, and operational requirements before broader adoption, leaving questions about implementation paths and metrics for the next step.
What puwipghooz8.9 Edge Really Is
Puwipghooz8.9 Edge is a term whose meaning remains unclear without broader context, but it can be described as a digital concept associated with a specific version or iteration of an edge-related technology.
The definition remains provisional, yet it anchors analysis around architecture, deployment, and governance. puwipghooz8.9 edge informs stakeholders about real world implications and potential security considerations.
How It Works in Real‑World Scenarios
In real-world deployments, puwipghooz8.9 Edge operates at the intersection of localized computation and centralized control, enabling data processing at or near the data source to reduce latency, bandwidth use, and exposure of sensitive information.
The approach highlights insight gaps and adoption challenges, requiring robust orchestration, standardized interfaces, and clear governance to ensure predictable performance and security across heterogeneous environments.
What It Means for Users and Businesses
What does puwipghooz8.9 Edge mean for users and businesses is best understood through its impact on performance, security, and cost. The analysis highlights Pujiitrame insights and Puwipghooz8.9 edge implications, providing objective assessments of latency, protection mechanisms, and total ownership expenses. Decisions should rest on measurable metrics, interoperability, and transparent risk management, preserving user autonomy and strategic resilience.
How to Evaluate Its Potential and Next Steps
How should organizations approach assessing its potential and charting next steps? The evaluation process is structured, evidence-based, and objective. It entails defining success metrics, collecting performance data, and comparing it to benchmarks. Key steps include risk assessment, feasibility, and cost-benefit analysis. The output highlights how to evaluate options and outlines potential steps for informed, freedom-oriented decision-making and strategic alignment.
Conclusion
Puwipghooz8.9 Edge embodies near-data processing with centralized governance, delivering lower latency, reduced bandwidth, and strengthened security through standardized orchestration. Real-world deployments hinge on robust interfaces and clear governance, with measurable risk controls guiding decisions. Anticipated objection: “edge adds cost without clear ROI.” Evidence-based response: empirical metrics—latency reductions, bandwidth savings, and governance gains—often justify investment when workloads demand rapid, localized responses. In sum, edge strategies align performance and protection within structured, evaluative frameworks, guiding strategic adoption and continuous optimization.