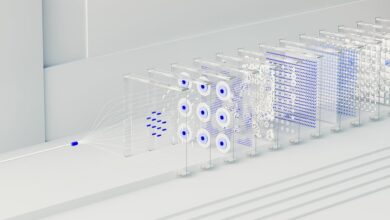
Neural Flow 2015475477 Cyber Node

Neural Flow 2015475477 Cyber Node acts as an edge-oriented processing unit that governs real-time data streams through localized scheduling and policy-driven orchestration. It emphasizes information flow, congestion signaling, and dynamic priority assignment to balance latency and throughput. The design addresses hardware heterogeneity, security, and resilience, ensuring deterministic performance and scalable monitoring across distributed, latency-constrained environments. Its relevance emerges from interoperability and failover guarantees, inviting scrutiny of deployment tradeoffs and practical constraints.
Explaining Neural Flow and Cyber Nodes
Neural Flow describes a framework in which data-driven computations propagate through interconnected processing units, forming a dynamic network that models information flow rather than static state. The concept centers on neural flow architectures where cyber nodes coordinate localized processing, enabling modular integration.
Data streams traverse combinational and iterative paths, highlighting edge deployability and resilience, while system-wide coherence emerges from disciplined, scalable orchestration.
How Cyber Nodes Orchestrate Real-Time Data Streams
Cyber nodes coordinate real-time data streams by enforcing localized scheduling, routing, and processing policies that align with global coherence objectives. They implement adaptive orchestration layers, calibrating timing, bandwidth, and compute resources across heterogeneous nodes. Tuning latency and robustness occur through dynamic priority assignment and congestion signaling.
Scalability strategies emphasize modularity, distributed control, and policy-driven replication to sustain consistent throughput under growth. Freedom-focused clarity guides engineering rigor.
Security, Resilience, and Edge Deployability of Neural Flow Nodes
Security, resilience, and edge deployability of Neural Flow nodes demand a rigorous assessment of threat models, fault tolerance, and deployment constraints. The analysis emphasizes formal security resilience mechanisms, distributed consensus checks, and failover continuity under heterogeneous environments. It evaluates adversarial surface reduction, data integrity, and authorization scopes, while considering edge deployability constraints, hardware heterogeneity, and latency budgets for autonomous, resilient operation.
Practical Applications and Deployment Considerations for Neural Flow 2015475477 Cyber Node
Practical deployment of the Neural Flow 2015475477 Cyber Node centers on capabilities, constraints, and integration pathways across diverse environments. The analysis evaluates neural networks applicability, edge inference efficiency, data streams handling, and governance of latency-sensitive tasks. Real time deployment considerations emphasize throughput, fault tolerance, and secure orchestration, ensuring interoperability, scalable monitoring, and deterministic performance within heterogeneous infrastructures and latency-constrained workloads.
Conclusion
In sum, Neural Flow 2015475477 Cyber Nodes function as disciplined arbiters of information, orchestrating edge compute with formalized policy and deterministic timing. Like a measured heartbeat in a distributed network, their scheduling, routing, and resilience mechanisms ensure predictable latency under diverse workloads. The architecture’s allusive symmetry—flow over state, locality over centrality—hints at a scalable future where heterogeneous devices synchronize through policy-driven, secure, and failproof edge ecosystems. The implied trajectory invites further exploration and rigorous validation.