Network Registry Overview About 41.62×24 and System Records

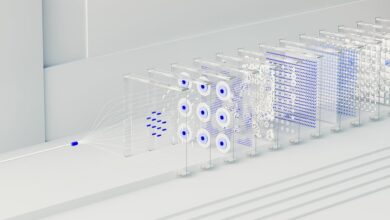
The Network Registry in 41.62×24 centers on a centralized ledger that catalogs devices, services, and configurations within scope. It preserves provenance through data lineage while enforcing privacy controls. System Records anchor digital assets to origins and state via an indexed map, linking events to a trusted ledger. Real-time audits provide ongoing visibility and gap detection, supporting disciplined governance. The approach offers interoperable interfaces and clear governance cadences, inviting careful consideration of next steps and potential implications.
What Is the Network Registry in 41.62×24?
The network registry in 41.62×24 serves as a centralized ledger that catalogs and indexes networked devices, services, and configurations within the system’s operational scope. It maintains provenance through data lineage records and enforces privacy controls to govern access. The registry supports auditable, transparent governance while preserving autonomy, enabling disciplined experimentation, freedom of configuration, and accountable interoperability across components.
How System Records Map Your Digital Assets
System records function as an indexed map that anchors digital assets to their origins, ownership, and state across the network.
They translate asset provenance into verifiable identifiers, linking events and transfers to a trusted ledger.
This structure supports a governance cadence, aligning stakeholders while preserving autonomy, transparency, and accountability within a cohesive registry that enables deliberate, freedom-respecting asset stewardship.
Real-Time Audits: Spot Gaps and Enforce Policies
Real-Time Audits enable continuous visibility into asset flows and governance compliance, revealing gaps that static records may overlook.
They support rigor in monitoring, validation, and remediation, turning scattered signals into actionable intelligence.
Real time audits enable timely responses, ensuring enforcement of policies and closure of deficiencies.
By highlighting deviations, they empower governance without constraining organizational autonomy, guiding disciplined freedom.
Spot gaps enforce policies.
Practical Use Cases and Next Steps With 41.62×24
Practical use cases for 41.62×24 address continuous governance, asset visibility, and regulatory alignment by applying structured workflows to real-time data. The approach supports data governance and explicit risk assessment, enabling proactive controls, auditability, and traceable decisions. It emphasizes modular deployment, interoperable interfaces, and measurable maturity.
Next steps involve piloting in critical domains, documenting outcomes, and refining governance metrics for scalable, freedom-respecting implementation.
Conclusion
In the registry’s quiet ledger, networks breathe as if etched in glass, each device a star chart and every event a measured pulse. System records cast a precise map, tracing origins through a disciplined lineage. Real-time audits glow like lighthouse beams, revealing gaps and guiding corrections with calm certainty. Within 41.62×24, governance becomes architecture—clear, modular, and interoperable—where provenance forms a sturdy backbone, and accountable interoperability sustains trustworthy, evolving digital assets across the spectrum.