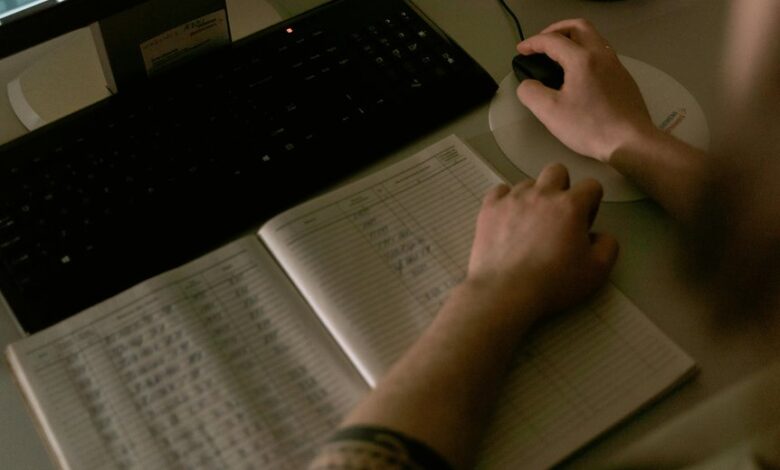
Cross-checking data entries across multiple sources requires disciplined governance of metadata, timestamps, and provenance. A standardized schema supports cross-source validation…
Read More »Messiturf100
A thorough review of the specified data records for verification requires a disciplined, criteria-driven approach. Each entry must be assessed…
Read More »The discussion on validating call tracking entries will focus on establishing a robust verification baseline across identifiers and references such…
Read More »This topic centers on confirming call log accuracy for a defined set of numbers and usernames. The goal is to…
Read More »Audit Incoming Call Records involves parsing a mixed set of candidate entries, distinguishing standard formats (IP:port, bare IP) from malformed…
Read More »The topic invites a careful, methodical review of incoming call details, focusing on IP-like values, port fragments, and inconsistent separators.…
Read More »This discussion examines incoming call data logs labeled as IP-annotated records, focusing on structure over content. The aim is to…
Read More »In assessing Verify-Ready Call Records, the entries listed—spanning numeric figures and IP-like identifiers—invite a methodical inspection of determinism, timestamps, and…
Read More »Authenticating call logs for accuracy requires a disciplined, methodical approach to each number—7322681119, 18774014903, 6014990935, 8088922955, 6156855230, 931225497, 6822404078, 3212741524,…
Read More »Cross-checking incoming call entries such as 8446866269, 3716941445, 7146059251, 8159895771, 18556991528, 4076127275, 18776922253, 7203722442, 4047379548, and 4698629324 demands a disciplined,…
Read More »