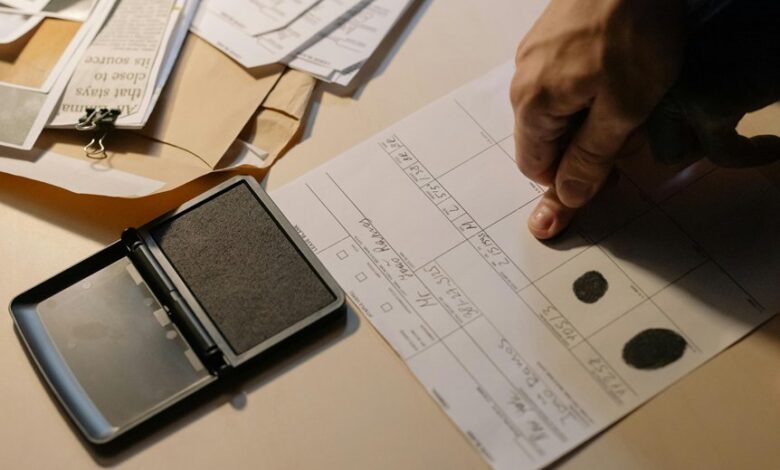
The user identifier cross-check log compiles cross-platform signals tied to Julietxxpanda, justinmartin666, Kengcomedu, Keybardtast, and mez64648219. The approach is methodical,…
Read More »Olivia
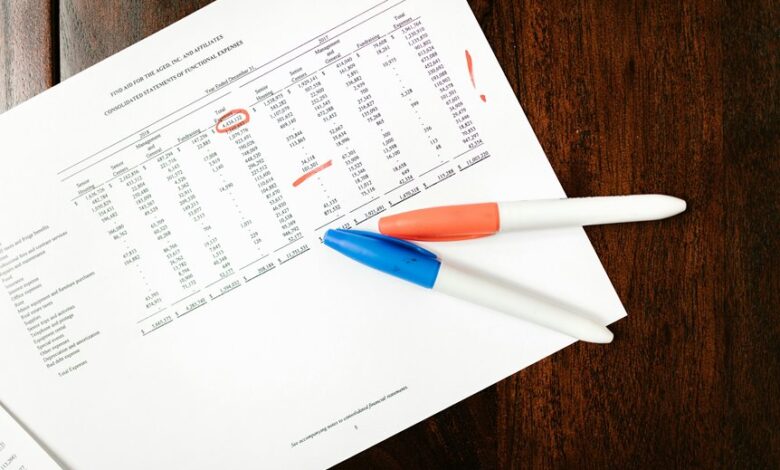
The Incoming Data Authenticity Review examines how data enters a system, focusing on source legitimacy, transit tamper-evidence, and fitness for…
Read More »The System Entry Validation Report outlines a standardized approach for Dtyrjy and partners to verify new components before integration. It…
Read More »The incoming communication record audit, led by anamedeiro99 and collaborators, seeks to establish objective metrics for inbox handling, logging, and…
Read More »The discussion centers on the Network Call Record Verification Set erl0001900 and its decoded identifiers, such as 103.194170.154, 111.190150.204, and…
Read More »Incoming call log validation for the ten target numbers requires a precise, auditable approach to capture who initiated each inbound…
Read More »Call Record Accuracy Inspection for the ten numbers establishes a disciplined, evidence-based review of each log entry. The process emphasizes…
Read More »The Incoming Call Data Verification Report for these numbers presents a structured view of provenance, lineage, and verification elements across…
Read More »Cross-checking incoming call entries requires a disciplined, methodical approach to verify legitimacy and consistency across the numbers listed. Each step—data…
Read More »The discussion centers on a formal review of call record authenticity for the listed numbers. It adopts a methodical, evidence-based…
Read More »